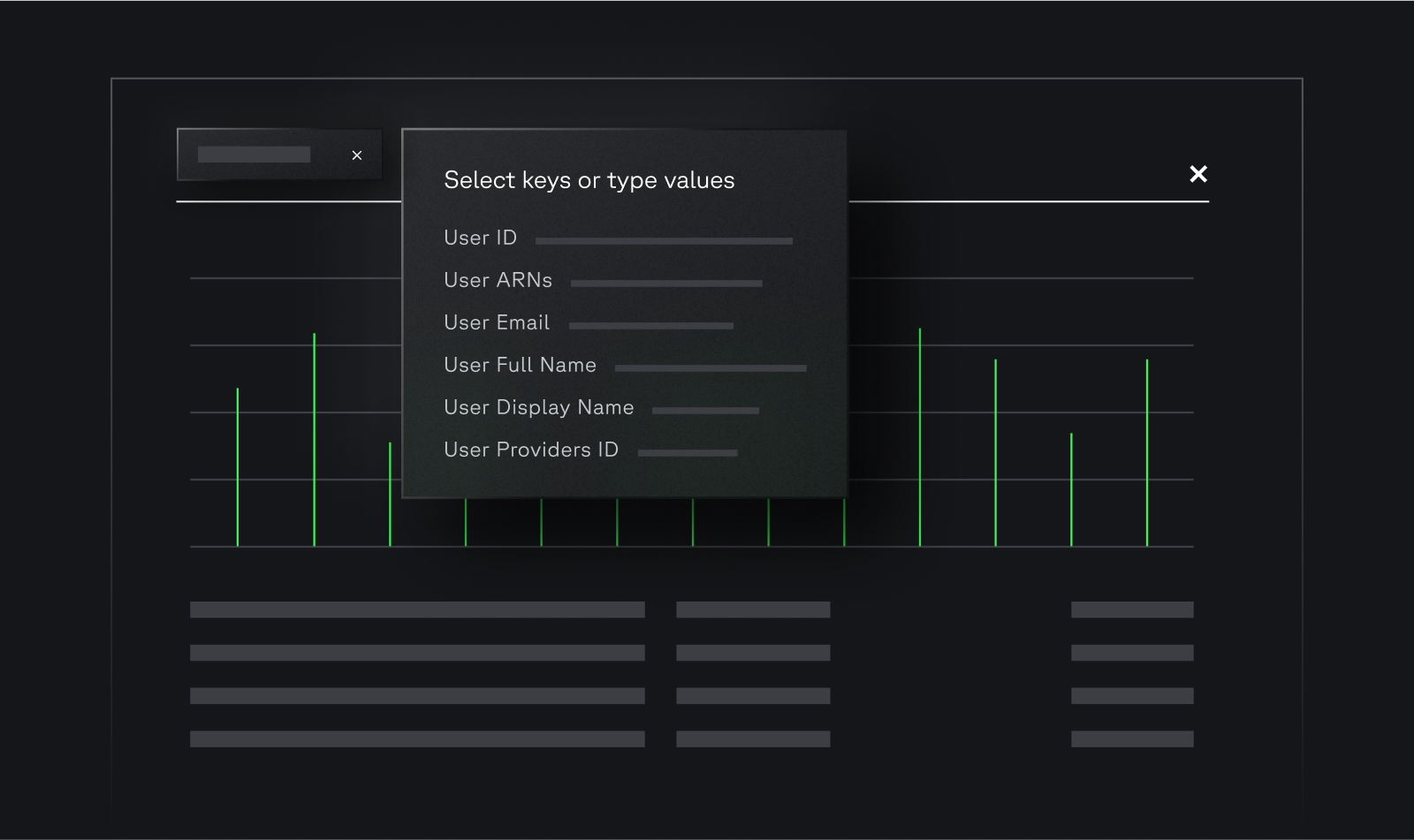
How It Works
Ingest All Logs for Full Visibility
Traditional SIEMs escalate costs when ingesting high-volume cloud logs like AWS CloudTrail, GuardDuty, EKS, ECS and VPCFlow. Panther offers cost-effective, searchable one-year data retention. With real-time detections and efficient search, it provides full visibility and leading threat-stopping capabilities.