PODCAST
How AI is changing the SOC operating model. Listen now →
close
How AI is changing the SOC operating model. Listen now →
close
How AI is changing the SOC operating model. Listen now →
close

The complete AI SOC platform
The complete AI SOC platform
With native access to your data, detections, and organizational knowledge — every decision makes your SOC smarter.
With native access to your data, detections, and organizational knowledge — every decision makes your SOC smarter.
Trusted by top security teams
Decisions don’t disappear.
They compound.
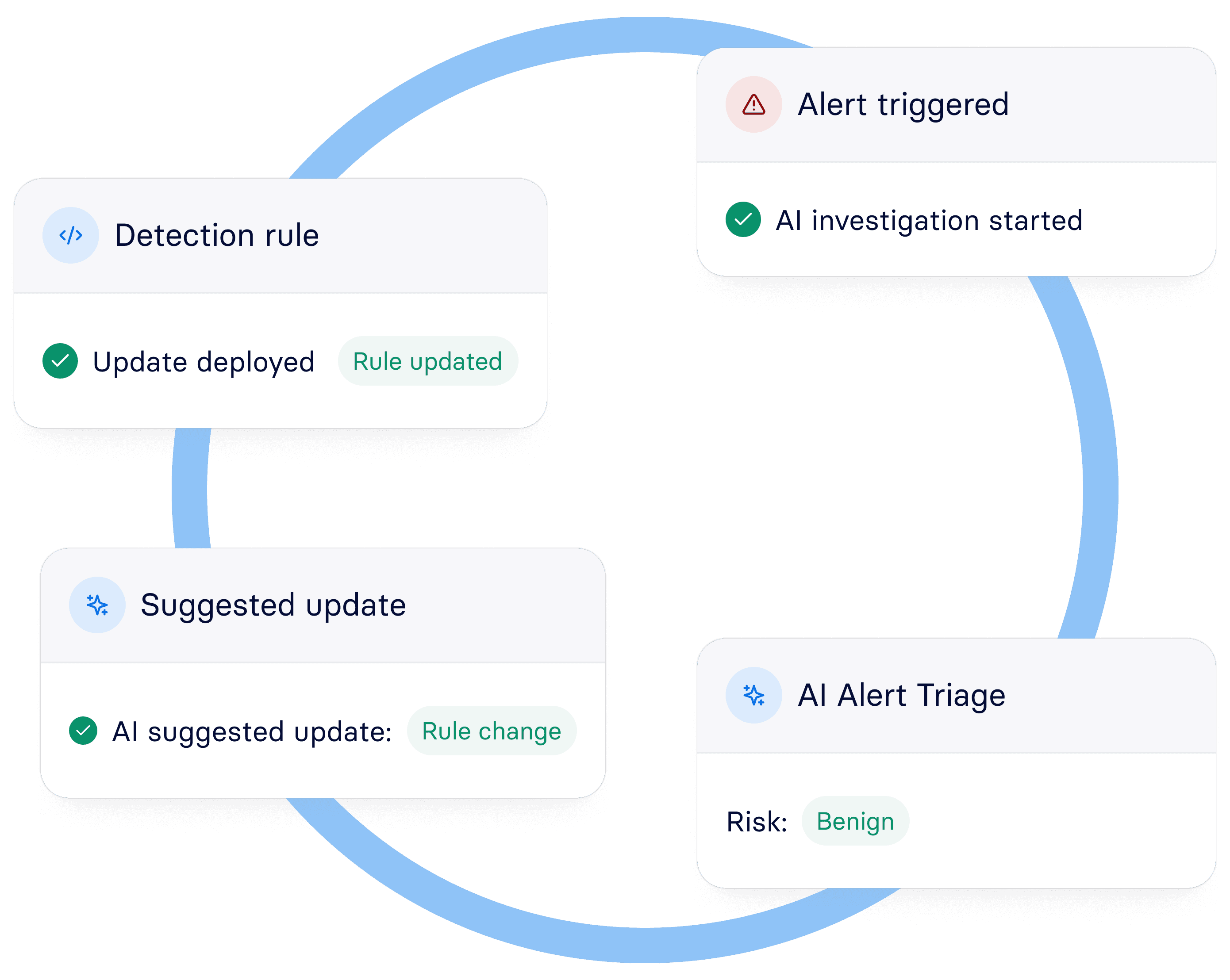
Panther connects your data lake, detection logic, and AI layer into a single closed-loop architecture, so when your team confirms an investigation outcome, that judgment feeds directly back into the detection that fired it. Every triage makes the next one better. The SOC gets smarter. The noise gets smaller.

Single prompt to full investigation
Panther AI doesn't summarize alerts and wait for instructions. It investigates, pivoting across your data lake, reviewing alert history, and pulling live context from your identity provider, code repos, and ticketing systems. Every investigation delivers a definitive risk classification with transparent reasoning, not a probability score.
Autonomous investigation. Complete context.
Definitive risk classification. Not a probability score.
Proactive coverage that expands beyond what you've written rules for.


Single prompt to full investigation
Panther AI doesn't summarize alerts and wait for instructions. It investigates, pivoting across your data lake, reviewing alert history, and pulling live context from your identity provider, code repos, and ticketing systems. Every investigation delivers a definitive risk classification with transparent reasoning, not a probability score.

Autonomous investigation. Complete context.
Definitive risk classification. Not a probability score.
Proactive coverage that expands beyond what you've written rules for.
Single prompt to full investigation
Panther AI doesn't summarize alerts and wait for instructions. It investigates, pivoting across your data lake, reviewing alert history, and pulling live context from your identity provider, code repos, and ticketing systems. Every investigation delivers a definitive risk classification with transparent reasoning, not a probability score.

Autonomous investigation. Complete context.
Definitive risk classification. Not a probability score.
Proactive coverage that expands beyond what you've written rules for.
“With Panther’s SIEM and AI SOC, we were able to stand up a fully deployed, in-house enterprise SOC in a matter of weeks.”
AVP, Cyber Defense & Engineering

“With Panther’s SIEM and AI SOC, we were able to stand up a fully deployed, in-house enterprise SOC in a matter of weeks.”
AVP, Cyber Defense & Engineering


Senior detection engineer in every seat.
Detections are only as good as the logic behind them. Panther is built on Python, not a proprietary query language or a black box, meaning every detection rule is readable, testable, version-controlled, and modifiable by AI. This is what makes the closed loop possible.
Describe a threat. Get a production-ready detection.
Detection-as-code. With the workflow your team already uses.
Every false positive makes your detections smarter.


Senior detection engineer in every seat.
Detections are only as good as the logic behind them. Panther is built on Python, not a proprietary query language or a black box, meaning every detection rule is readable, testable, version-controlled, and modifiable by AI. This is what makes the closed loop possible.

Describe a threat. Get a production-ready detection.
Detection-as-code. With the workflow your team already uses.
Every false positive makes your detections smarter.
Senior detection engineer in every seat.
Detections are only as good as the logic behind them. Panther is built on Python, not a proprietary query language or a black box, meaning every detection rule is readable, testable, version-controlled, and modifiable by AI. This is what makes the closed loop possible.

Describe a threat. Get a production-ready detection.
Detection-as-code. With the workflow your team already uses.
Every false positive makes your detections smarter.
70%
Faster
detection tuning

70%
Faster
detection tuning

70%
Faster
detection tuning

85%
Faster
detection tuning

85%
Faster
detection tuning

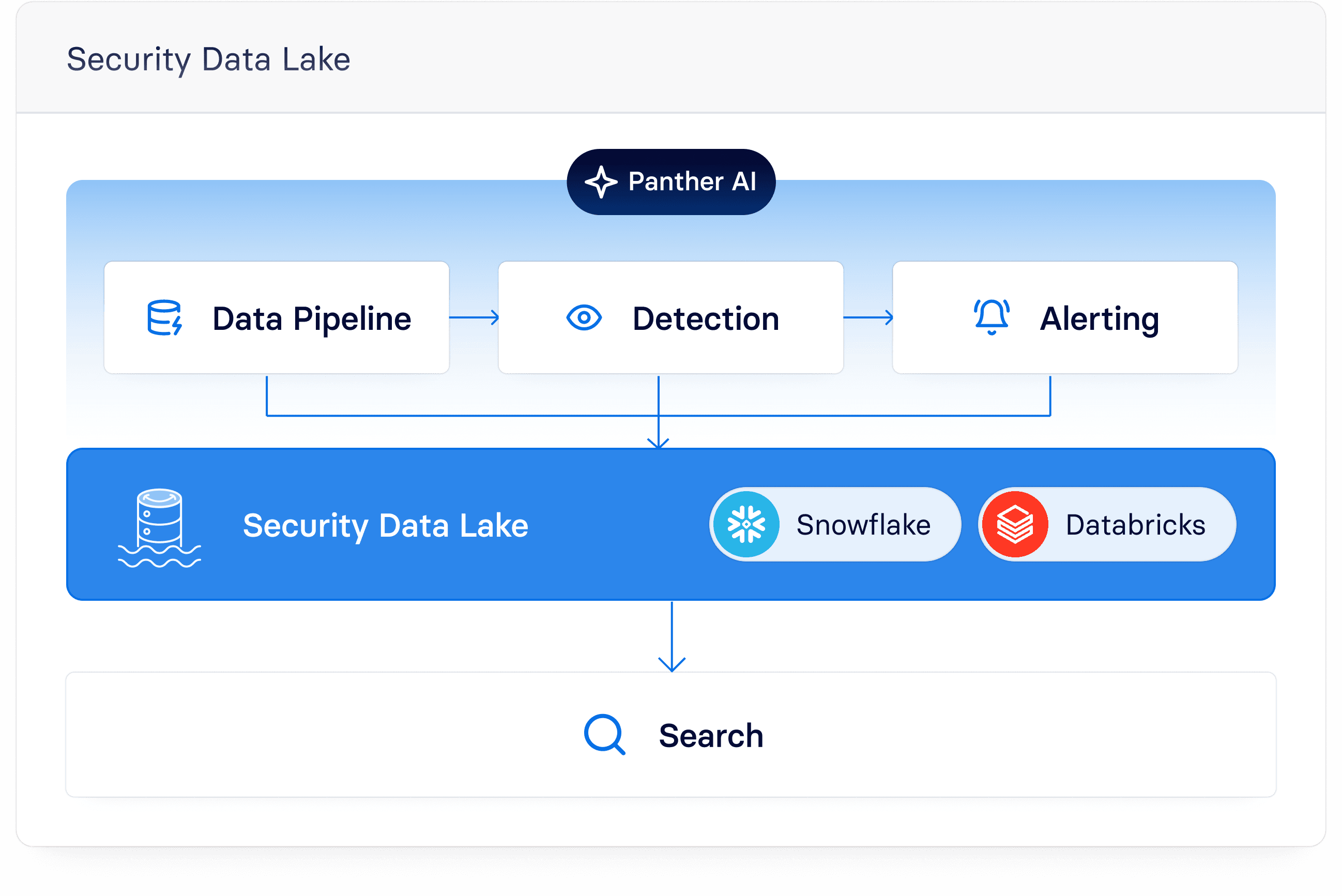
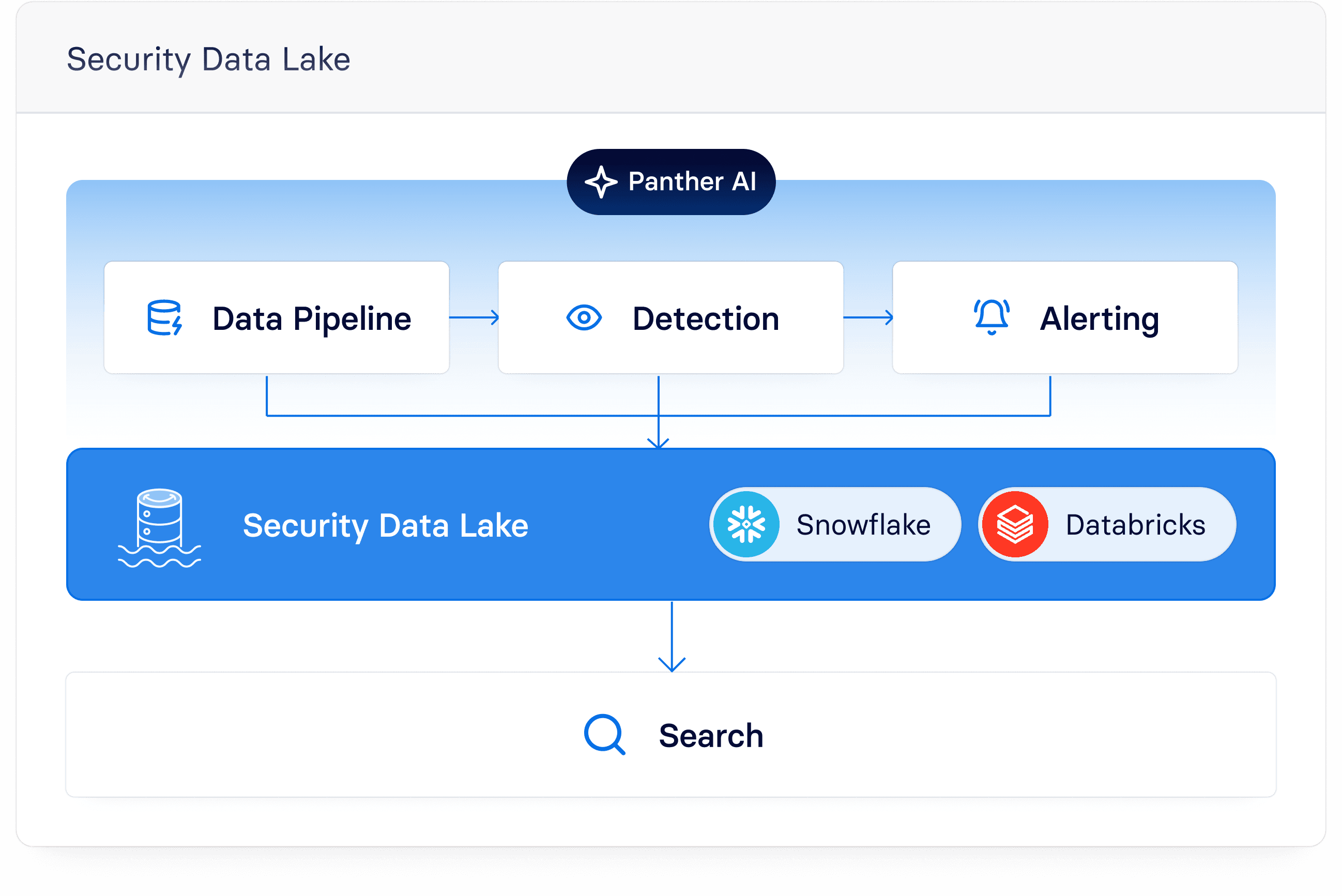
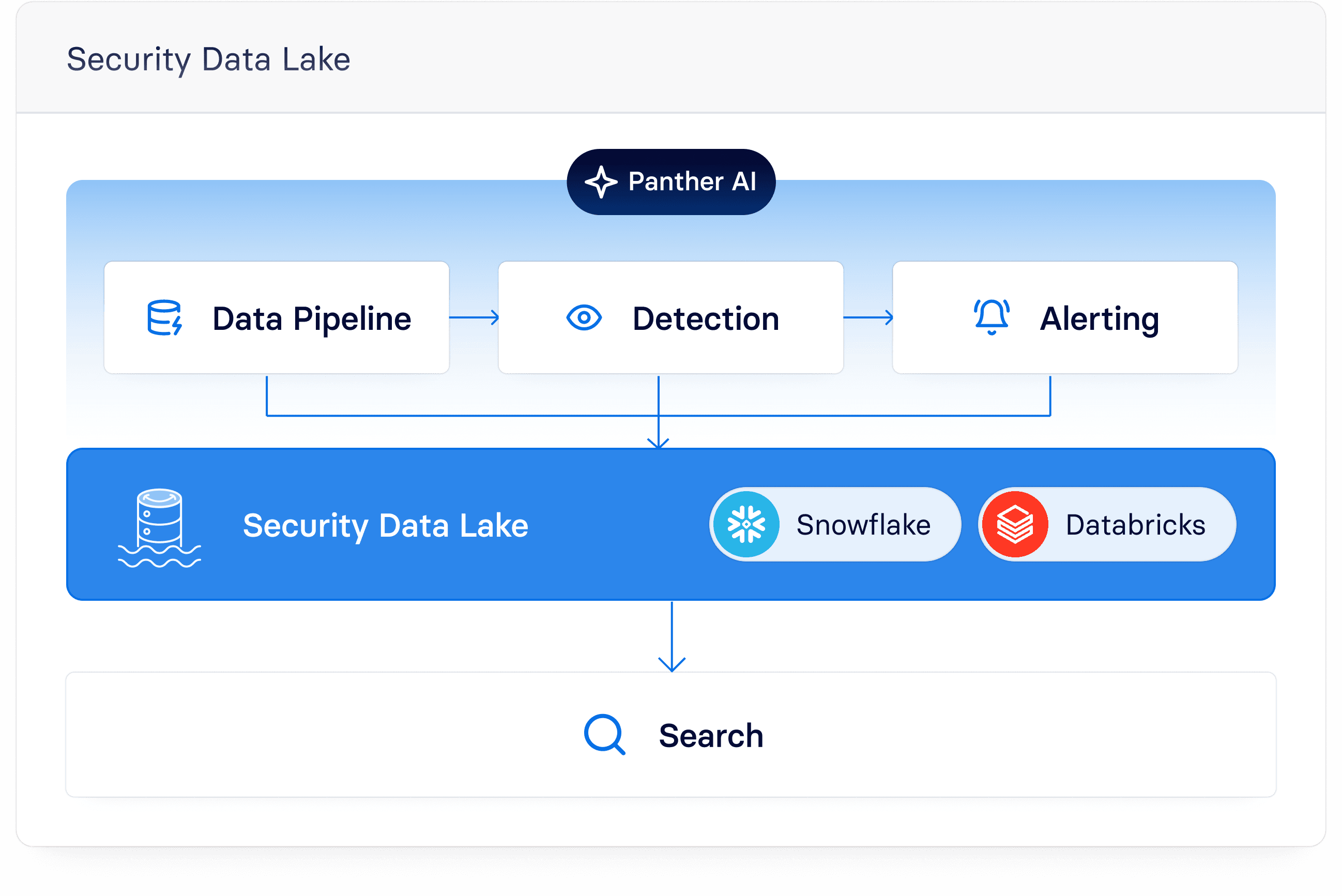
All your security data. In one place. Yours to keep.
Your data lives in your own Snowflake or Databricks instance — no vendor lock-in, no ingestion budgets forcing you to leave logs behind, no retention policies limiting what Panther AI can pivot across during an investigation. The foundation of the closed loop is complete data.
Ingest from anything. Normalized on the fly
No proprietary query language, no vendor lock-in.
Full visibility into your security program.
All your security data. In one place. Yours to keep.
Your data lives in your own Snowflake or Databricks instance — no vendor lock-in, no ingestion budgets forcing you to leave logs behind, no retention policies limiting what Panther AI can pivot across during an investigation. The foundation of the closed loop is complete data.
Ingest from anything. Normalized on the fly
No proprietary query language, no vendor lock-in.
Full visibility into your security program.
All your security data. In one place. Yours to keep.
Your data lives in your own Snowflake or Databricks instance — no vendor lock-in, no ingestion budgets forcing you to leave logs behind, no retention policies limiting what Panther AI can pivot across during an investigation. The foundation of the closed loop is complete data.
Ingest from anything. Normalized on the fly
No proprietary query language, no vendor lock-in.
Full visibility into your security program.


5x
More
log data ingested


5x
More
log data ingested

3.5x
Increase
security log visibility

3.5x
Increase
security log visibility
Every alert makes the next one easier.
Panther's closed-loop architecture captures every triage outcome, every investigation, every detection improvement and feeds it back into the system. Alert volume drops, and institutional knowledge stops living in senior analysts' heads and starts living in the platform.
Alert quality loop
Institutional Knowledge, encoded.
Coverage that grows on autopilot.
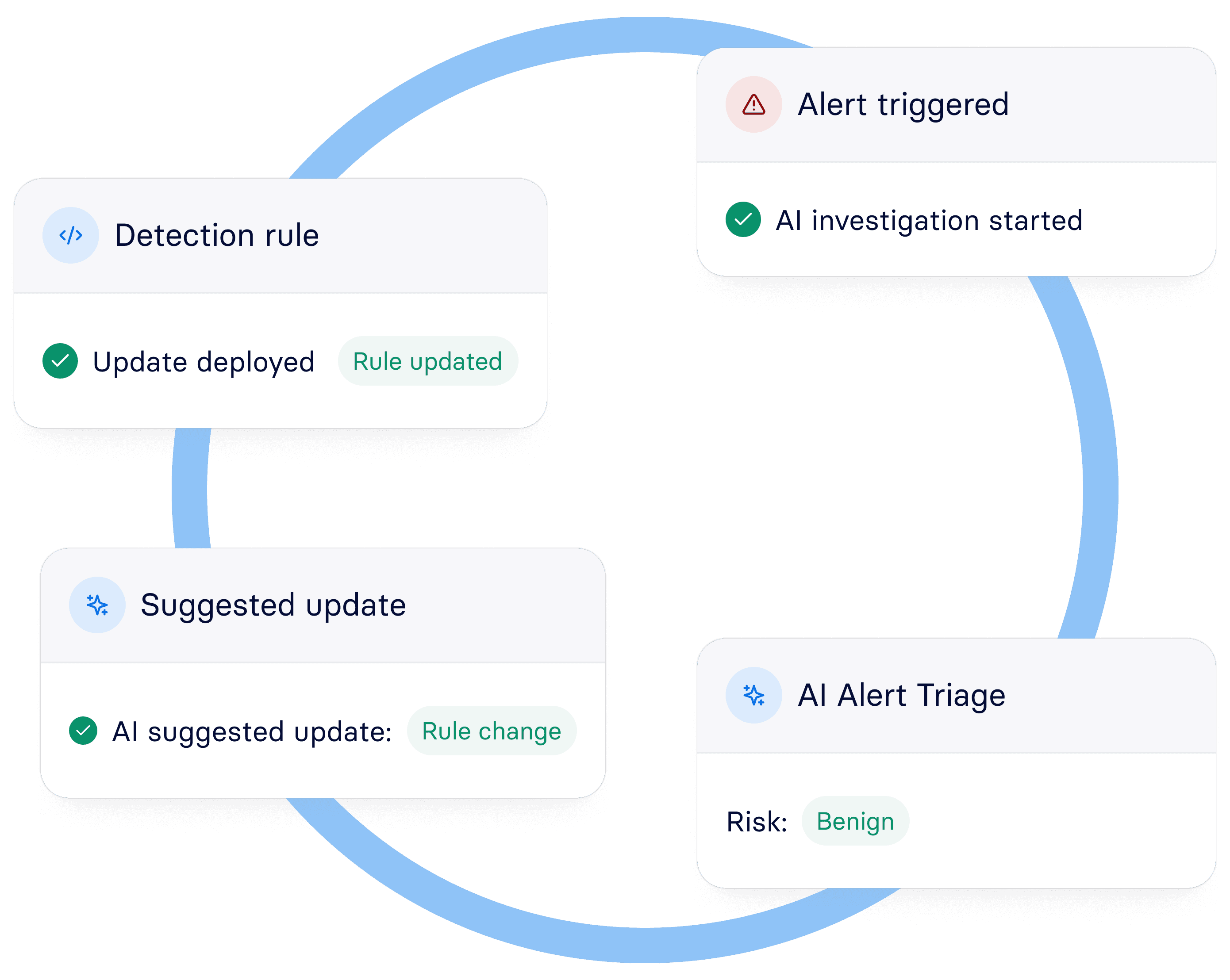

Every alert makes the next one easier.
Panther's closed-loop architecture captures every triage outcome, every investigation, every detection improvement and feeds it back into the system. Alert volume drops, and institutional knowledge stops living in senior analysts' heads and starts living in the platform.
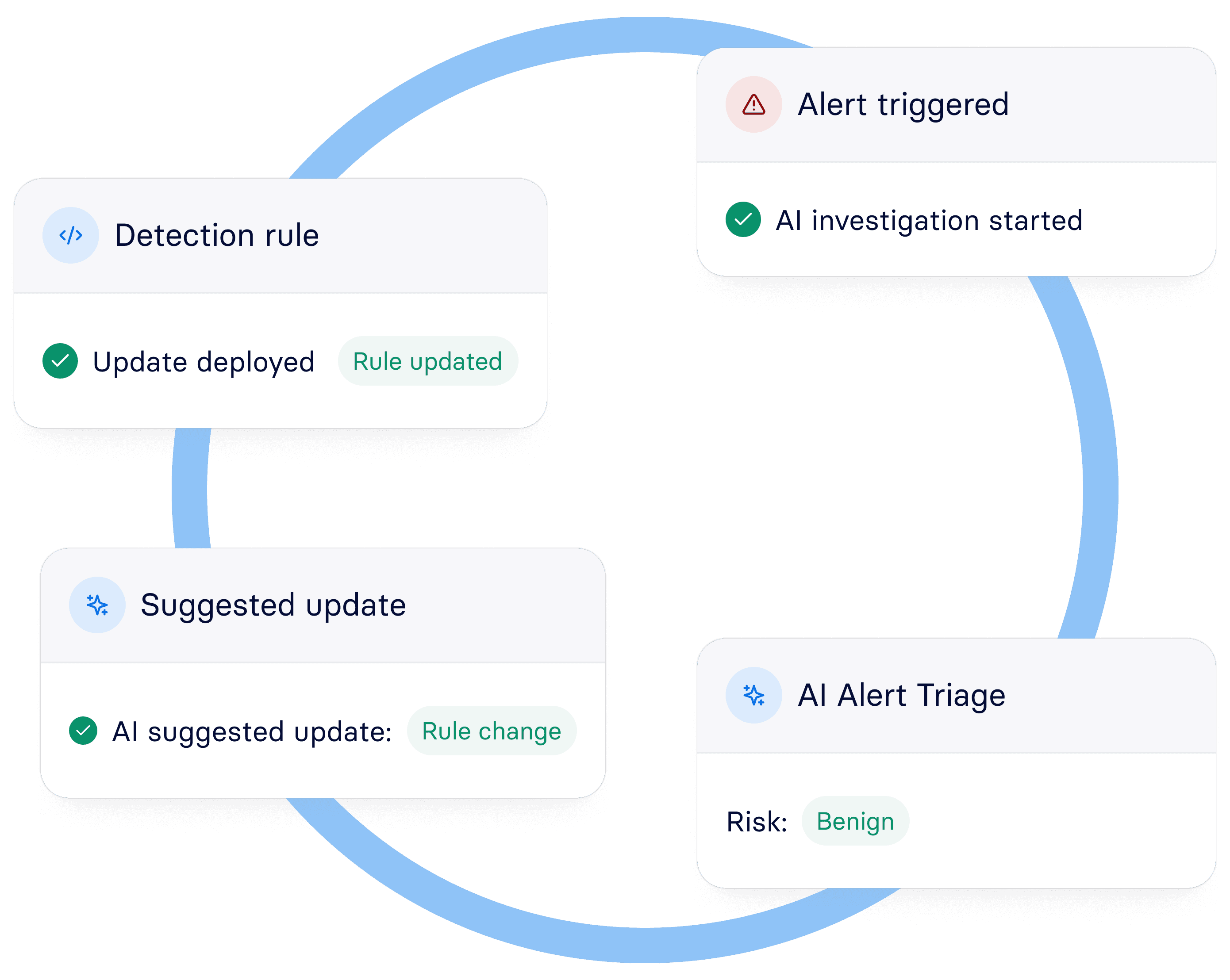
Alert quality loop
Institutional Knowledge, encoded.
Coverage that grows on autopilot.
Every alert makes the next one easier.
Panther's closed-loop architecture captures every triage outcome, every investigation, every detection improvement and feeds it back into the system. Alert volume drops, and institutional knowledge stops living in senior analysts' heads and starts living in the platform.
Alert quality loop
Institutional Knowledge, encoded.
Coverage that grows on autopilot.
“Panther learns from how our analysts respond. That's what actually closes the loop.”
Christian Nomi Peterson, Product Security Manager at nCino

“Panther learns from how our analysts respond. That's what actually closes the loop.”
Christian Nomi Peterson, Product Security Manager at nCino

Built together. Not bolted on.
Panther was built cloud-native in 2018 on Python, SQL, and structured data lakes — not because it was trendy, but because it was right. Those same choices turned out to be exactly what large language models need to be effective.

Security Data Lake
Your data, your warehouse. Snowflake or Databricks. No vendor lock-in. Petabyte scale, predictable pricing.

Detection Engine
Python detection-as-code. Version controlled, CI/CD, peer reviewed. Readable and modifiable by AI. The loop closes here.

AI Agent layer
Specialized agents with native access to detection logic, data lake, and organizational context. Read, reason, propose, execute.

Built together. Not bolted on.
Panther was built cloud-native in 2018 on Python, SQL, and structured data lakes — not because it was trendy, but because it was right. Those same choices turned out to be exactly what large language models need to be effective.

Security Data Lake
Your data, your warehouse. Snowflake or Databricks. No vendor lock-in. Petabyte scale, predictable pricing.

Detection Engine
Python detection-as-code. Version controlled, CI/CD, peer reviewed. Readable and modifiable by AI. The loop closes here.

AI Agent layer
Specialized agents with native access to detection logic, data lake, and organizational context. Read, reason, propose, execute.

Built together. Not bolted on.
Panther was built cloud-native in 2018 on Python, SQL, and structured data lakes — not because it was trendy, but because it was right. Those same choices turned out to be exactly what large language models need to be effective.

Security Data Lake
Your data, your warehouse. Snowflake or Databricks. No vendor lock-in. Petabyte scale, predictable pricing.

Detection Engine
Python detection-as-code. Version controlled, CI/CD, peer reviewed. Readable and modifiable by AI. The loop closes here.

AI Agent layer
Specialized agents with native access to detection logic, data lake, and organizational context. Read, reason, propose, execute.

Built together. Not bolted on.
Panther was built cloud-native in 2018 on Python, SQL, and structured data lakes — not because it was trendy, but because it was right. Those same choices turned out to be exactly what large language models need to be effective.

Security Data Lake
Your data, your warehouse. Snowflake or Databricks. No vendor lock-in. Petabyte scale, predictable pricing.

Detection Engine
Python detection-as-code. Version controlled, CI/CD, peer reviewed. Readable and modifiable by AI. The loop closes here.

AI Agent layer
Specialized agents with native access to detection logic, data lake, and organizational context. Read, reason, propose, execute.


Open data lake. Snowflake or Databricks. You own your data.
Open data lake. Snowflake or Databricks. You own your data.

Detection-as-code. Readable and modifiable by AI. Not a black box.
Detection-as-code. Readable and modifiable by AI. Not a black box.

MCP integrations. Native context from Atlassian, GitHub, Jira, Notion & more.
MCP integrations. Native context from Atlassian, GitHub, Jira, Notion & more.

Full audit trails. Every AI action visible, logged, and auditable.
Full audit trails. Every AI action visible, logged, and auditable.

Configurable thresholds. Humans stay in control. AI handles the volume.
Configurable thresholds. Humans stay in control. AI handles the volume.
Run it your way.
Panther gives you full flexibility in how you deploy without compromising on capability, security, or data ownership.

Panther Cloud
Fully managed by Panther. We handle infrastructure, scaling, and maintenance so your team stays focused on security, not ops.

Panther Cloud
Fully managed by Panther. We handle infrastructure, scaling, and maintenance so your team stays focused on security, not ops.

Panther Cloud
Fully managed by Panther. We handle infrastructure, scaling, and maintenance so your team stays focused on security, not ops.

Bring your own AWS & Data Lake
Deploy Panther in your own cloud environment with your existing AWS and Databricks or Snowflake accounts. Full control, full data ownership, same complete platform.

Bring your own AWS & Data Lake
Deploy Panther in your own cloud environment with your existing AWS and Databricks or Snowflake accounts. Full control, full data ownership, same complete platform.
Built for the full security lifecycle.
Built for the full security lifecycle.

Complete context
Native access to everything an agent needs. Your data lake, detection code, alert history, enrichments, runbooks, and external tools via MCP; all in a single workflow.

Compounding intelligence
Every alert makes the system smarter. Panther learns from your team's decisions and encodes that knowledge into the platform.

Proactive coverage
Your team can now hunt like experts. Build detections in natural language and hunt across your data lake, without detection engineering bottlenecks.

Autonomous action
From prompt to investigation, and beyond. Clear risk classification, benign alert closure, detection improvements—all with audit trails.

Autonomous action
From prompt to investigation, and beyond. Clear risk classification, benign alert closure, detection improvements—all with audit trails.

What happens when
teams run on Panther.
What happens when
teams run on Panther.

85%
Reduction
in false positives

85%
Reduction
in false positives

90%
Reduction
in investigation time

90%
Reduction
in investigation time

90%
Reduction
in investigation time

90%
Reduction
in investigation time
70%
Reduction
alert volume

70%
Reduction
alert volume

85%
Reduction
in alert volume

85%
Reduction
in alert volume



80%
Auto resolved
alerts


80%
Auto resolved
alerts


80%
Auto resolved
alerts

“Panther learns from how our analysts respond. That's what actually closes the loop.”
Product Security Manager


“Panther learns from how our analysts respond. That's what actually closes the loop.”
Product Security Manager


“Panther’s AI Alert Triage puts everything I need in a single place.”
Staff Security Engineer


“Panther’s AI Alert Triage puts everything I need in a single place.”
Staff Security Engineer

Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.


Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.
Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.


Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.


Get product updates, webinars, and news
By submitting this form, you acknowledge and agree that Panther will process your personal information in accordance with the Privacy Policy.
Platform
Solutions
All rights reserved © 2026 Panther, Inc
Get product updates, webinars, and news
By submitting this form, you acknowledge and agree that Panther will process your personal information in accordance with the Privacy Policy.
Platform
Solutions
All rights reserved © 2026 Panther, Inc
Get product updates, webinars, and news
By submitting this form, you acknowledge and agree that Panther will process your personal information in accordance with the Privacy Policy.
Platform
Solutions
All rights reserved © 2026 Panther, Inc