PODCAST
How AI is changing the SOC operating model. Listen now →
close
How AI is changing the SOC operating model. Listen now →
close
How AI is changing the SOC operating model. Listen now →
close
Data Pipeline
All your security data,
in one place.
Native connectors, automatic normalization, and petabyte-scale ingestion.

Trusted by top security teams


Flexible, high-scale ingestion. Easily ingest logs across your environment, at petabyte scale with pricing that doesn't punish growth.
Flexible, high-scale ingestion. Easily ingest logs across your environment, at petabyte scale with pricing that doesn't punish growth.

No vendor lock-in. Your security data stays in Snowflake or Databricks. Queryable, portable, and free from proprietary formats.
No vendor lock-in. Your security data stays in Snowflake or Databricks. Queryable, portable, and free from proprietary formats.

Complete context, every investigation. Every investigation automatically draws on the full picture of your environment.
Complete context, every investigation. Every investigation automatically draws on the full picture of your environment.
Complete Visibility
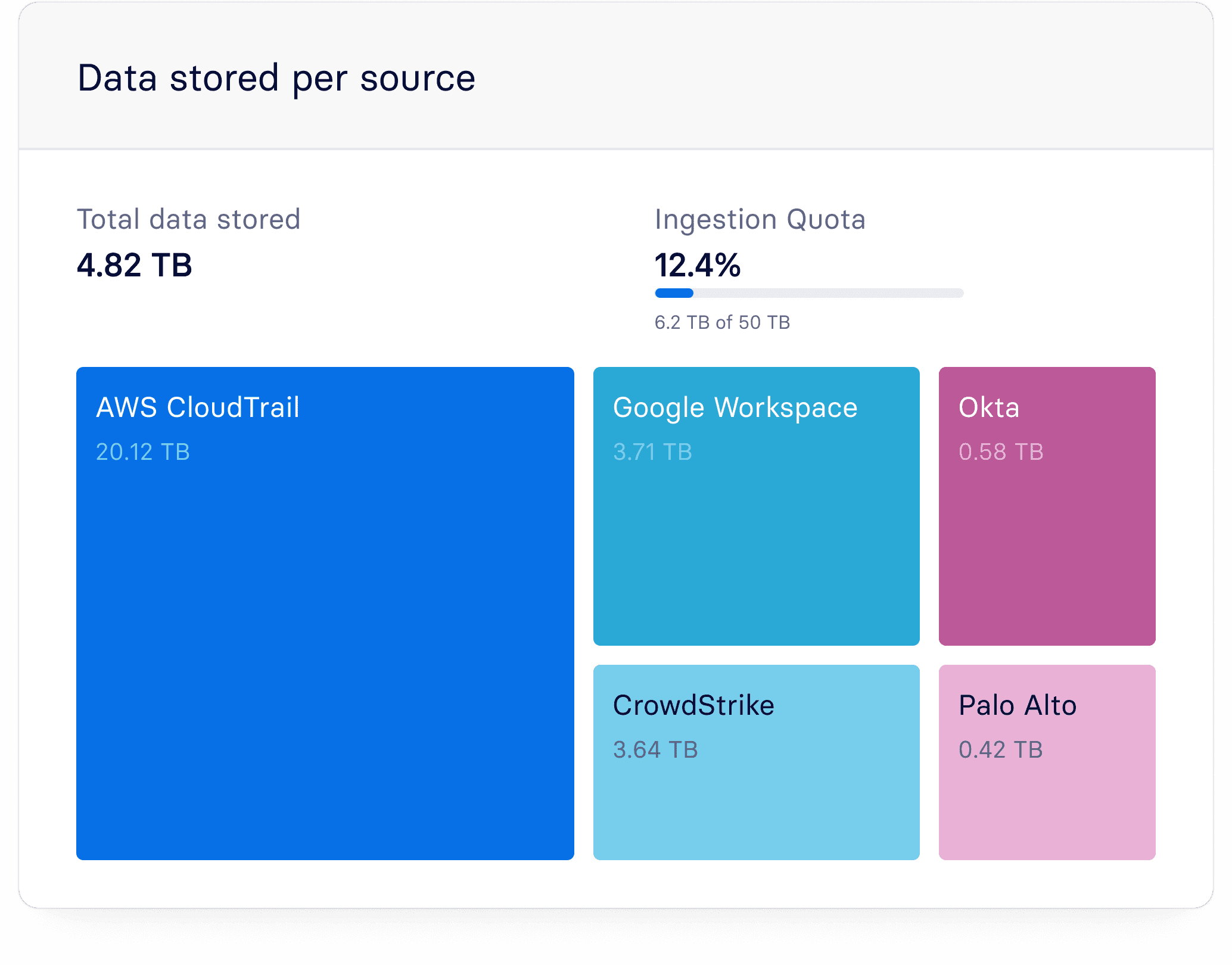
Ingest every source without cost tradeoffs
Ingest every log source without cost tradeoffs, eliminating unknown blind spots and protecting your entire environment.



Unified Context
All your security data in a single queryable layer
Every log source is immediately accessible, normalized, and ready to query — so your team spends time on analysis, not data collection.






Data-Grounded AI
Deterministic AI findings
The quality of every AI finding is a direct reflection of the data underneath it, and Panther investigates against a complete, normalized dataset every time.



Compounding Intelligence
Control what reaches your data lake.
Filter low-value events before they consume quota, and use transformations to reshape data at ingest so detections and threat hunting queries run against clean, structured logs.



Built for security data at scale.
Built for security data at scale.
Pre-built Integrations
AI Schema Builder
Log Forwarding Agent
Natural Language Query
Petabyte-Scale Ingestion
Data Normalization
Pre-built Integrations
Native integrations for the tools your team already uses like AWS, Okta, CrowdStrike, Slack, and more.


Pre-built Integrations
Native integrations for the tools your team already uses like AWS, Okta, CrowdStrike, Slack, and more.

Pre-built Integrations
Native integrations for the tools your team already uses like AWS, Okta, CrowdStrike, Slack, and more.

AI Schema Builder
Automatically generate schemas for any source, turning data into structured, queryable security intelligence without manual configuration.

AI Schema Builder
Automatically generate schemas for any source, turning data into structured, queryable security intelligence without manual configuration.

Bring Your Own Data Lake
Panther runs natively on your Snowflake or Databricks instance, keeping your security data in infrastructure you already own and control.

Bring Your Own Data Lake
Panther runs natively on your Snowflake or Databricks instance, keeping your security data in infrastructure you already own and control.

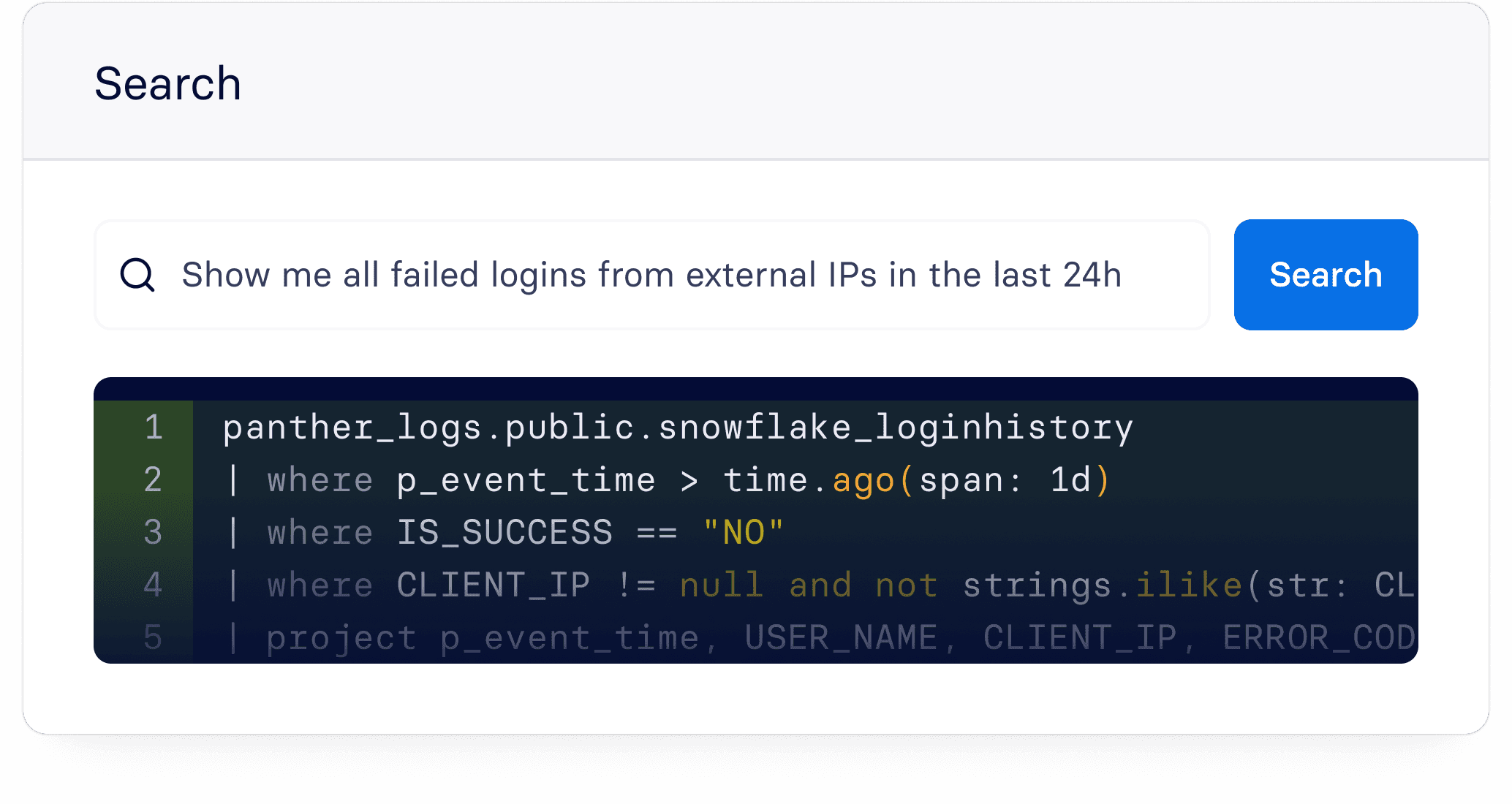
Natural Language Query
Search across all your security data in plain English, SQL, or PantherFlow — no proprietary query language to learn.
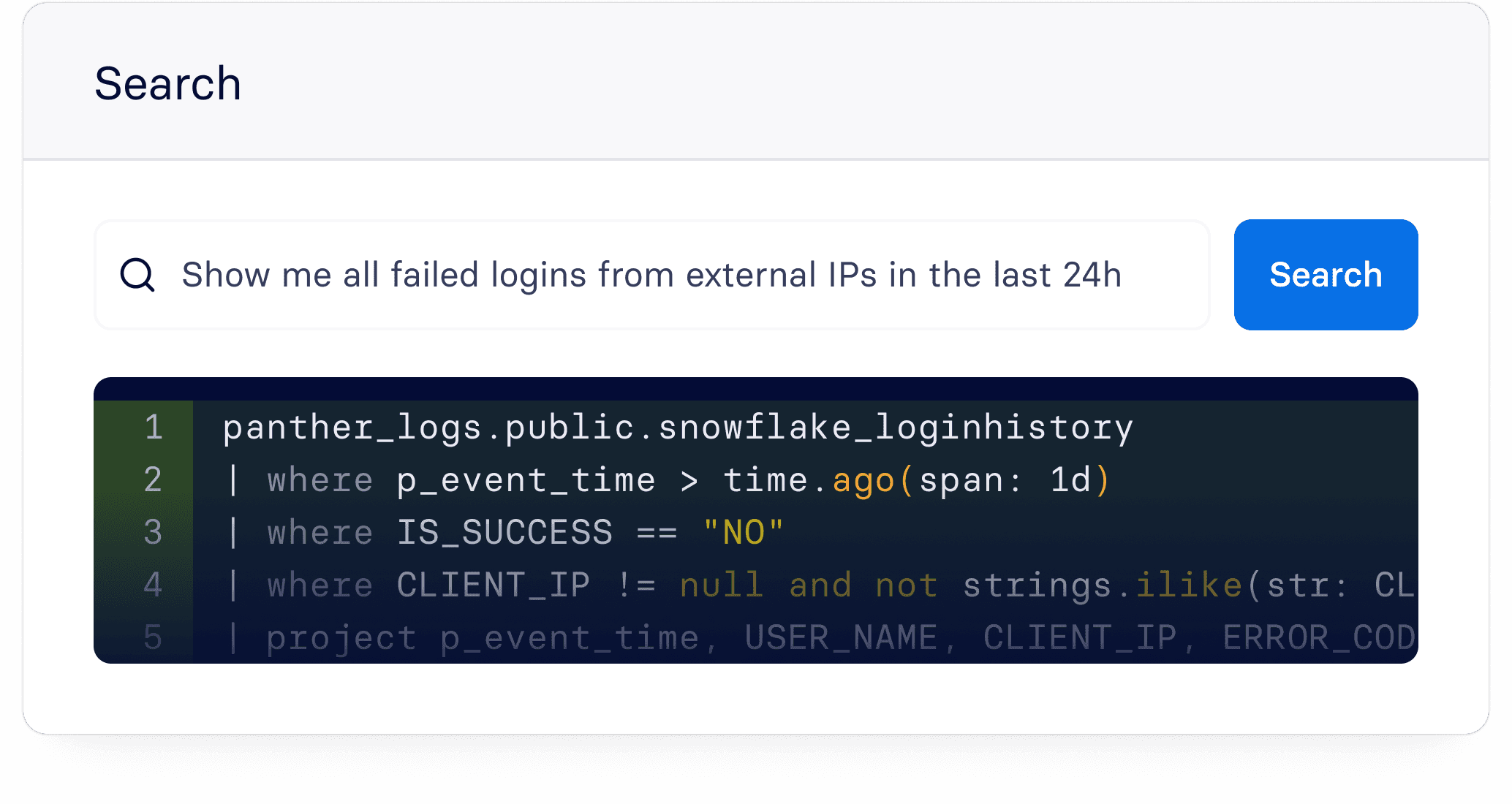
Natural Language Query
Search across all your security data in plain English, SQL, or PantherFlow — no proprietary query language to learn.
Petabyte-Scale Ingestion
Ingest at any volume without performance degradation or pricing surprises as your environment grows.
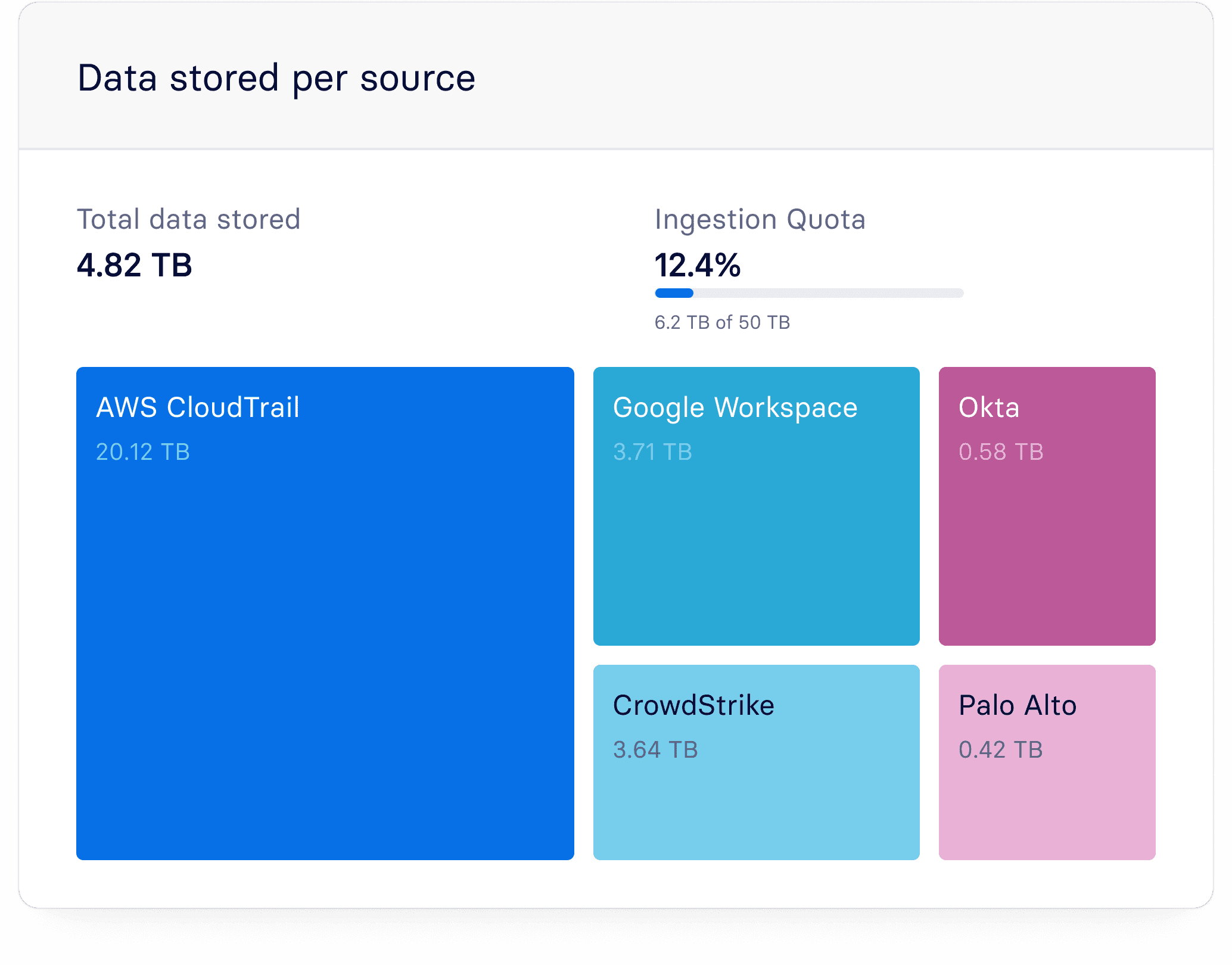
Petabyte-Scale Ingestion
Ingest at any volume without performance degradation or pricing surprises as your environment grows.
Data Normalization
Log data is normalized at ingest, so every source is immediately structured, queryable, and ready for detection and investigation.

Data Normalization
Log data is normalized at ingest, so every source is immediately structured, queryable, and ready for detection and investigation.

HealthEquity reduced investigation times by 90% with Panther. That's data-grounded AI in production.

Proof from teams
who’ve been there.
Proof from teams
who’ve been there.
5x
More log data ingested

5x
More log data ingested

"Now, we have 365 days of hot storage and an intuitive interface for searching. There's no more back and forth with auditors. It just works."

"Now, we have 365 days of hot storage and an intuitive interface for searching. There's no more back and forth with auditors. It just works."

9x
More data ingestion
9x
More data ingestion
"With Panther, we went from not wanting to monitor any more log sources to actively searching for more logs to bring in. That's the difference between an effective tool and a tool that builds confidence."
90%
Infrastructure visibility achieved

90%
Infrastructure visibility achieved

"Log source onboarding is ridiculously smooth. Fast. Almost fun. I never thought I could hit 90 percent visibility in just a few months."

5x
More log data ingested

"Now, we have 365 days of hot storage and an intuitive interface for searching. There's no more back and forth with auditors. It just works."

9x
More data ingestion
"With Panther, we went from not wanting to monitor any more log sources to actively searching for more logs to bring in. That's the difference between an effective tool and a tool that builds confidence."
90%
Infrastructure visibility achieved

"Log source onboarding is ridiculously smooth. Fast. Almost fun. I never thought I could hit 90 percent visibility in just a few months."

Learn more about Panther
Learn more about Panther
Explore the Platform
Alert Triage & Automation
Panther doesn't summarize alerts and wait for instructions — it investigates.
Detection Engine
Native access to your detection logic means every triage outcome feeds back into the rules that fire.
AI SOC Agent
An agent that runs on a schedule, responds to natural language queries, and takes action with complete context.
Analytics & Reporting
Built-in dashboards and MITRE ATT&CK mapping, from alert trends to program maturity.
Data Pipeline
All your security data, in one place.
Explore the Platform
Alert Triage & Automation
Panther doesn't summarize alerts and wait for instructions — it investigates.
Detection Engine
Native access to your detection logic means every triage outcome feeds back into the rules that fire.
AI SOC Agent
An agent that runs on a schedule, responds to natural language queries, and takes action with complete context.
Analytics & Reporting
Built-in dashboards and MITRE ATT&CK mapping, from alert trends to program maturity.
Data Pipeline
All your security data, in one place.
Explore the Platform
Alert Triage & Automation
Panther doesn't summarize alerts and wait for instructions — it investigates.
Detection Engine
Native access to your detection logic means every triage outcome feeds back into the rules that fire.
AI SOC Agent
An agent that runs on a schedule, responds to natural language queries, and takes action with complete context.
Analytics & Reporting
Built-in dashboards and MITRE ATT&CK mapping, from alert trends to program maturity.
Data Pipeline
All your security data, in one place.
Explore the Platform
Alert Triage & Automation
Panther doesn't summarize alerts and wait for instructions — it investigates.
Detection Engine
Native access to your detection logic means every triage outcome feeds back into the rules that fire.
AI SOC Agent
An agent that runs on a schedule, responds to natural language queries, and takes action with complete context.
Analytics & Reporting
Built-in dashboards and MITRE ATT&CK mapping, from alert trends to program maturity.
Data Pipeline
All your security data, in one place.
Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.


Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.
Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.


Bolt-on AI closes alerts. Panther closes the loop.
See how Panther compounds intelligence across the SOC.


Get product updates, webinars, and news
By submitting this form, you acknowledge and agree that Panther will process your personal information in accordance with the Privacy Policy.
Platform
Solutions
All rights reserved © 2026 Panther, Inc
Get product updates, webinars, and news
By submitting this form, you acknowledge and agree that Panther will process your personal information in accordance with the Privacy Policy.
Platform
Solutions
All rights reserved © 2026 Panther, Inc
Get product updates, webinars, and news
By submitting this form, you acknowledge and agree that Panther will process your personal information in accordance with the Privacy Policy.
Platform
Solutions
All rights reserved © 2026 Panther, Inc



