BLOG
Sober Up! npm Typosquat Delivers Winos4.0 Implant via Multi-Stage PowerShell Dropper
Alessandra
Rizzo
Introduction
The Panther Threat Research Team identified a malicious npm package trevlo delivering a Winos4.0 framework implant to Windows developer workstations. The campaign, active since April 5, 2026, uses a classic typosquat of Express.js to lure developers into installing a multi-stage trojan dropper.
The package's postinstall hook silently executes an obfuscated JavaScript loader that spawns a base64-encoded PowerShell command, which in turn fetches and executes a second-stage PowerShell script from attacker-controlled infrastructure. That script downloads and runs a Winos4.0 stager binary (CodeRun102.exe) with full evasion, complete with hidden window execution, Zone Identifier removal, and process detachment.
This campaign is notable for two reasons. First, it represents a new delivery vector for Winos4.0, a post-exploitation framework previously distributed exclusively through fake gaming utilities and SEO-poisoned installers targeting Chinese and Vietnamese-speaking users. Delivery via npm supply chain marks an expansion toward developer-targeted operations. Second, the campaign arrives amid a sustained surge in npm supply chain attacks and a growing tail of opportunistic typosquat packages, making it easy for an implant to hide in the noise.
The package accumulated 866 downloads over the past month. The C2 domain (welovechinatown[.]info) remains active at time of writing.
Campaign Overview
The campaign was first identified through our automated npm scanning pipeline on April 06, 2026.
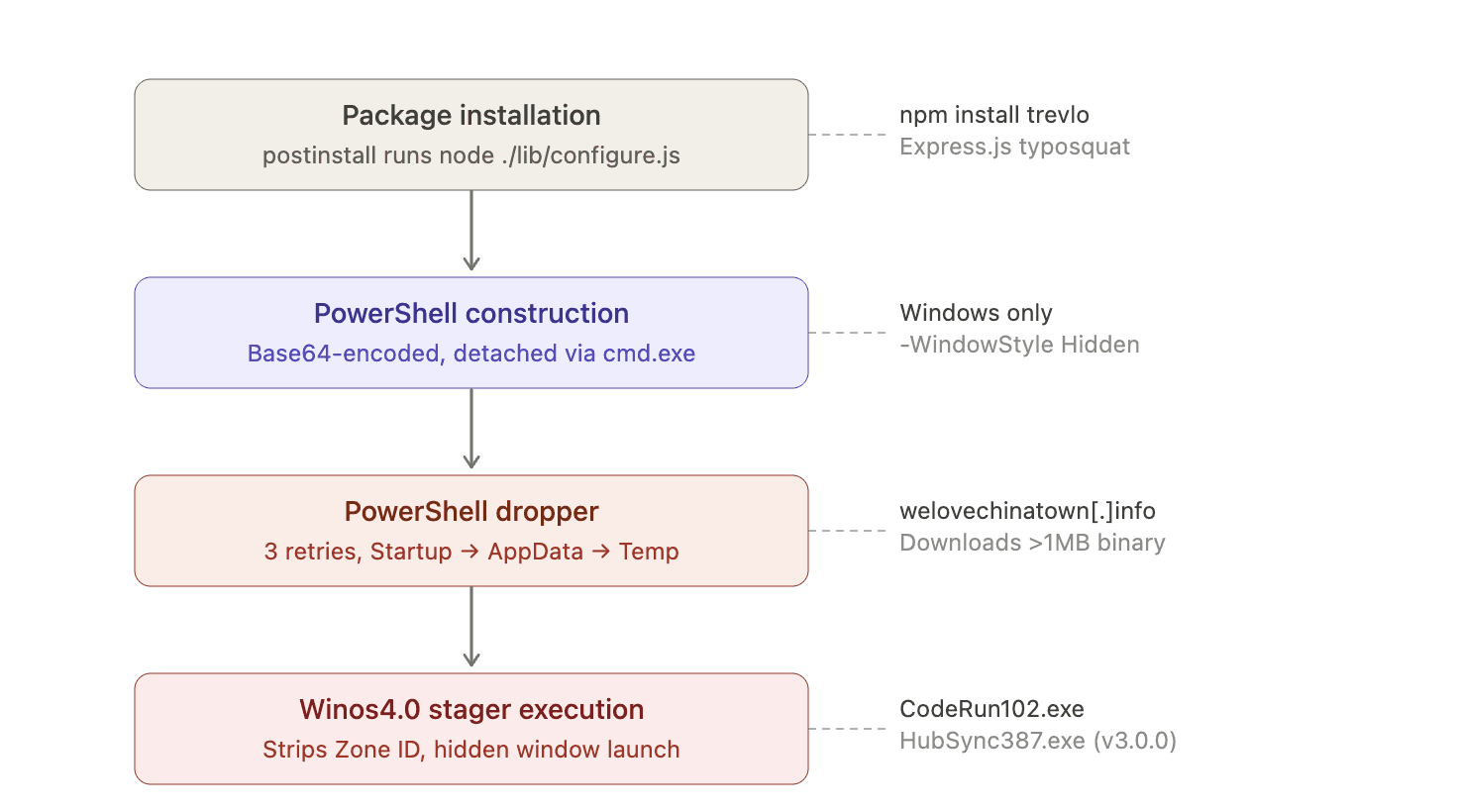
The attack proceeds in four stages:
Stage 1: Package installationnpm install trevlo triggers a postinstall hook that runs node ./lib/configure.js.
Stage 2: PowerShell constructionlib/configure.js checks for Node.js ≥ 18 and os.platform() === 'win32'. On Windows, it builds a Base64-encoded PowerShell command, spawns it through cmd.exe with -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass, detaches with .unref(), and silently catches all errors with catch(_){}.
Stage 3: PowerShell dropper The first-stage fetches and executes a second script from the C2. This dropper attempts to download the Winos4.0 binary into four directories in order: Startup, %APPDATA%, %LOCALAPPDATA%, %TEMP%. Each location is retried 3 times with randomized delays. The binary must exceed 1 MB to proceed.
Stage 4: Winos4.0 execution The dropper strips the NTFS Zone Identifier ADS, sets the file attribute to Hidden, and launches via [Diagnostics.Process]::Start() with WindowStyle='Hidden'. The binary is a Winos4.0 stager that connects to C2, retrieves the Login Module DLL, and bootstraps the full framework.
Final Payload: Winos4.0
The final payload is a Winos4.0 stager, an open-source post-exploitation framework representing an advanced evolution of the Gh0strat malware. While previous campaigns using Winos4.0 have been attributed to Chinese-nexus actors, the framework's public availability means tooling alone cannot support attribution.
Winos4.0 provides operators with:
Remote Control: Full remote shell access.
Surveillance: Keylogging, taking screenshots of the desktop and specific apps like WeChat or banking sites, and recording audio.
Data Theft: Stealing files, browser data, and cryptocurrency wallet information.
We confirmed through sandboxed execution that the payload downloaded by the PowerShell dropper harvested browser credentials, injected into browser processes, and targeted cryptocurrency wallet extensions.
Previous Winos4.0 campaigns (Silver Fox, Void Arachne, CleverSoar) distributed the framework via fake gaming utilities, driver assistants, and SEO-poisoned search results, primarily targeting Chinese and Vietnamese-speaking end users. The trevlo campaign represents a pivot: npm supply chain delivery targeting developers regardless of language or region.
Infrastructure Analysis
The first C2 domain we encountered, gusikkwski[.]top was registered on April 11, 2026, whereas the newest, welovechinatown[.]info on April 21, 2026, less than 18 hours before trevlo@4.0.0 , the latest version, was published to npm.
|
| |
|---|---|---|
Registrar | NameSilo | Registrar ID 303.0 / rdapserver.net |
Nameservers | dnsowl.com (NameSilo default) | Cloudflare |
Privacy method | NameSilo WHOIS privacy (all fields blank) | Garbage hex strings, Seychelles jurisdiction, disposable email |
Created | April 11, 2026 | April 21, 2026 |
Status | serverHold (taken down) | Active |
gusikkwski[.]top was suspended (serverHold), likely prompting the rotation to welovechinatown[.]info for v4.0.0.
Detection Guidance
Process creation monitoring: Alert on cmd.exe or powershell.exe spawned as a child of node.exe with -WindowStyle Hidden or -EncodedCommand arguments. In CI/CD environments, this pattern should never occur during legitimate npm install operations.
Network monitoring: Monitor for outbound HTTPS connections to welovechinatown[.]info from developer workstations or build agents. DNS queries for this domain from any internal host are a high-fidelity indicator.
File system monitoring: Watch for creation of executables in the Windows Startup folder by non-interactive processes, and for deletion of Zone.Identifier alternate data streams — a strong signal of Mark-of-the-Web bypass.
npm audit: Organizations should audit their dependency trees for the trevlo package. Run npm ls trevlo across all projects and CI/CD lockfiles. The package should be added to internal block lists immediately.
Endpoint detection: The presence of %TEMP%\\c2_build_err.log on any Windows host is a confirmed indicator of compromise for this campaign. The log file persists even if the dropper fails.
Conclusion
The trevlo campaign shows npm supply chain attacks evolving as a delivery mechanism for post-exploitation frameworks. Express.js typosquatting paired with a Winos4.0 payload is a step up from the credential stealers and cryptominers that characterize most malicious npm packages. The payload itself is commodity, focused on browser credentials and crypto wallets, but the delivery mechanism is the escalation.
The volume of npm supply chain attacks creates cover for more capable payloads. Defenders should treat any postinstall-triggered compromise as a potential entry point for post-exploitation frameworks, beyond simple credential stealers.
See it in action
Most AI closes the alert. Panther closes the loop.

Indicators of Compromise
Network IOCs
Type | Value |
|---|---|
Domain |
|
Domain |
|
URL |
|
URL |
|
URL |
|
URL |
|
Host IOCs
Type | Value | |
|---|---|---|
File name |
| |
File name |
| |
File name |
| |
File location |
| |
File location |
| |
File location |
| |
File location |
| |
File attrib | Hidden | |
Log file |
| |
ADS removal |
| |
SHA256 | 1b64d83bf86db293ea1204ee7fad62784858b537ec9ba7baff792926cb687033 | Winos4.0 Payload |
SHA256 | 00b6b59157aa87f181a6a8e2b21a84aed40f8c8343b39aff660afca6161492b6 | Winos4.0 Payload |
SHA256 | cb6567ca182b9ec02d50d76030838f36754e65aeb209e19e679d24634f6b276b | Winos4.0 Payload |
SHA256 | d904260f11adbcca96bf0234fb45719bb79c526375ecbc99cb374d50364f8100 | PowerShell Dropper Script |
SHA256 | 3cab147aaf2004ef2fda916c54a8439712e6acae2c18dac4c10509aa42567087 | PowerShell Dropper Script |
SHA256 | 71cb918d22e98ac486e6f1142530a1529f198ec8c982da595e24d75e9c1d1c43 | PowerShell Dropper Script |
Package IOCs
Type | Value |
|---|---|
npm package |
|
npm account |
|
| |
Tarball |
|
Payload |
|
SHA256 Tarball |
|
Commands
Share:
RESOURCES






