How It Works
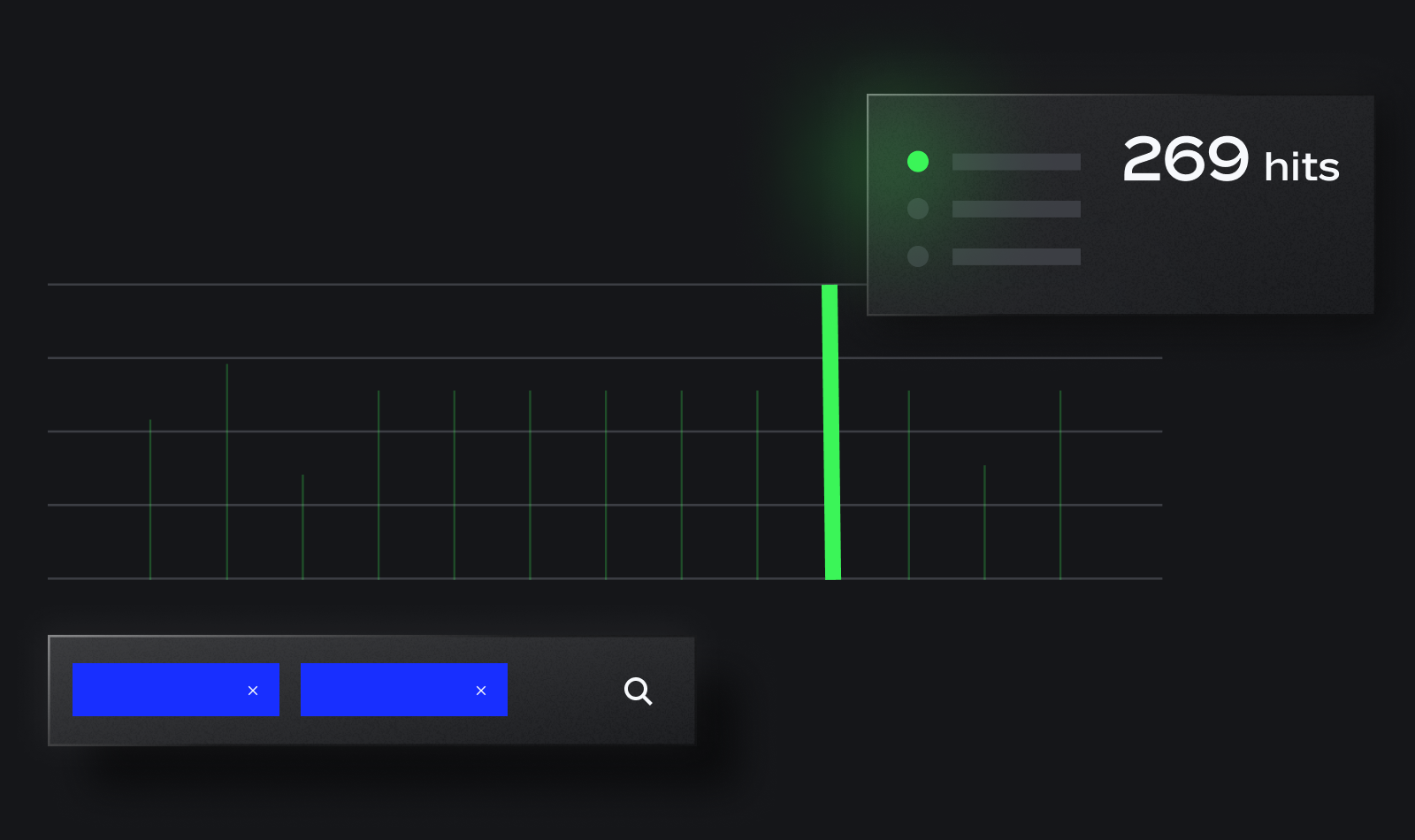
Cross-Log Queries
Don’t let a legacy SIEM restrict your searches to a single log type. Panther allows searches across multiple log types, providing insights into correlated events across threat vectors. This enables deeper analysis of log data to identify security incident root causes.